Cloud incident response at UNSW with digital forensics powered by AWS
AWS Public Sector Blog
MARCH 11, 2024
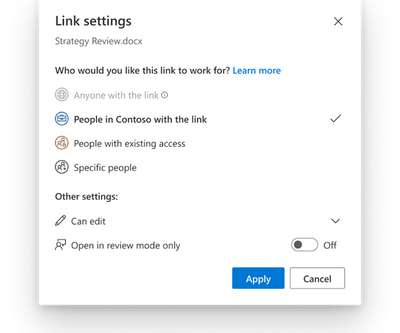
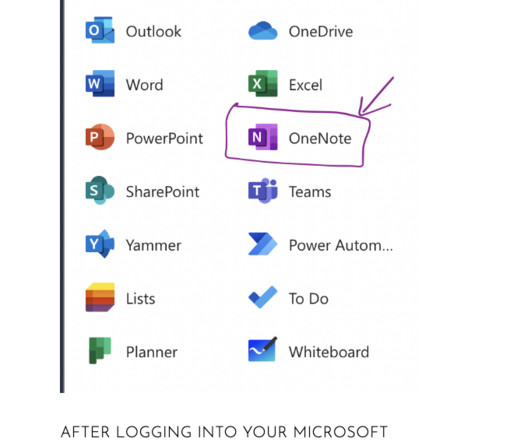
Users assign a set of key-value tags to the instance to trigger the automation steps for each instance. For example, when GuardDuty detects a potential malicious event, the IR administrator can apply the workload instance with the tag to trigger the functions. Simplified view of the JIT access provisioning process.




































Let's personalize your content